Configure Alteryx Server Authentication
Configure the authentication method you want to use to manage Server access on the System Settings > Gallery Authentication page.
Start by selecting the authentication method you want to use for your Server. Then, go to the setup steps for your selected method.
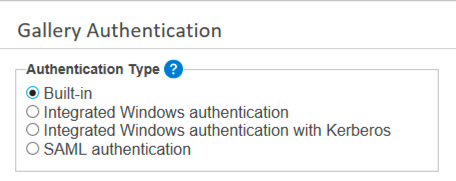
Select Your Authentication Type
Server supports built-in authentication, integrated Windows authentication with or without Kerberos support, and SAML authentication.
Built-in: Users specify an email address and password of their choosing to access the Server.
Integrated Windows authentication: Users access the Server with internal network credentials.
Integrated Windows authentication with Kerberos: Users access the Server with internal network credentials using Kerberos authentication protocols. The setup process for both Integrated Windows authentication and Integrated Windows authentication with Kerberos are the same. For more information, go to Complete the Set Up for Your Selected Authentication Type and choose Set Up Integrated Windows Authentication.
SAML authentication: Users access the Server with Identity Provider (IDP) credentials.
Aviso
Server doesn't support changing the authentication type after configuration. Doing so might compromise the Server functionality. If you want to change the authentication type, contact your account team to discuss options for assistance.
Complete the Set Up for Your Selected Authentication Type
The set up for each authentication type varies. Select your selected authentication type for steps to complete the setup.
Step 1. Set a Default Gallery Administrator for Built-in Authentication
After selecting Built-in authentication, create a Default Gallery Administrator at the bottom of the Gallery Authentication page. The Gallery (Server) administrator manages users, workflows, and more. For Built-in authentication, enter the administrator's email address.
Complete the remaining screens in System Settings (go to the Server UI and Engine help pages for more info on these screens),and select Finish.
Step 2. Finish the Gallery Administrator Account Creation
To complete the creation of the Gallery administrator account, go to the sign-in page of the Server. To do so, select the link to the Server shown on the System Settings > Status page or enter the URL to the Server in your internet browser.
Select Sign In.
On the sign-in page, select Don't have an account? Create one now.
Enter a First Name and Last Name, and select a timezone from the drop-down menu.
In Email, enter the email address that you provided for the Default Gallery Administrator on the System Settings > Gallery Authentication page.
In Password, create an account password. Your password must contain:
At least 8 characters
At least 1 letter
At least 1 number
Uppercase and lowercase letters
At least 1 special character
Select Sign Up.
You are now logged in as the Gallery (Server) administrator. The credentials you entered in the sign-up form are saved as your credentials going forward. You are now ready to add Server users. Go to Add Server Users.
Importante
If you are using AWS with Windows Authentication, the TCP connection has to maintain the same source port to stay authenticated. For this reason, we recommend using either the network or classic load balancer rather than application load balancer.
Nota
The difference in setting up the Integrated Windows Authentication and Integrated Windows Authentication with Kerberos is the protocol which is used to authenticate users with Active Directory. The Integrated Windows Authentication option uses NTLM while the Integrated Windows Authentication with Kerberos replaces NTLM with Kerberos.
No special configuration within Server itself is needed but the Kerberos option requires a properly configured Kerberos realm and KDC to be present in the Active Directory domain.
Step 1. Set a Default Gallery Administrator for Windows Authentication
After selecting Integrated Windows authentication, create a Default Gallery Administrator at the bottom of the Gallery Authentication page. The Gallery (Server) administrator manages users, workflows, and more. For Integrated Windows authentication, enter the user account in this format: domain\username.
Complete the remaining screens in System Settings (go to the Server UI and Engine help pages for more info on these screens),and select Finish.
Step 2. Access the Server
The default Gallery (Server) administrator can now access the Server. To do so, select the link to the Server shown on the System Settings > Status page or enter the URL to the Server in your internet browser. You are now logged in as the Gallery (Server) administrator and ready to add Server users. Go to Add Server Users.
Multi-Domain Support
Server supports multiple domains for Windows authentication. You don't need to configure anything in Server to enable this, but these capabilities and permissions have to be present across the domains.
The domain the Server runs on needs to have the same trust policy as other domain users so Active Directory can resolve and determine user permissions.
Both domains need to be part of the same forest.
The Alteryx service needs to be able to read all attributes from CN=Users and CN=Computers containers for both domains. The Alteryx service runs under the local system account on the server it is installed on. If you define a dedicated service account instead of using the local system, the account has to have permission to read all attributes from both containers to enable authentication for both domains.
To configure SAML authentication for Single Sign On (SSO), your Identity Provider (IDP) has to support SAML.
Importante
Before configuring SAML authentication for the Server, you have to add Server as a Service Provider in the IDP. The IDP might need...
the ACS Base URL (for example,
http://localhost/aas/Saml2/Acs).the SP Entity ID (for example,
http://localhost/aas/Saml2).The IDP might also require that you map email, firstName, and lastName attribute statements to corresponding fields in the IDP to authenticate users.
The IDP Signing Certificate should be configured with a signing algorithm of SHA-256 or greater.
Select an option for obtaining metadata required by the IDP. You can configure SAML using an IDP Metadata URL or an X509 certificate and IDP SSO URL.
Complete the SAML IDP Configuration.
ACS Base URL: The URL for the Assertion Consumer Service that accepts SAML messages to establish a session.
IDP URL: The URL for the Alteryx application configured in the IDP, also known as, the IDP Entity ID.
IDP Metadata URL: The URL provided by the IDP that includes the IDP SSO URL and the X509 certificate for configuring the Alteryx Authentication Service.
IDP SSO URL: The SSO URL, provided by the IDP, that the Alteryx Authentication Service uses to log into the IDP.
X509 certificate: The public certificate provided by the IDP for secure communication with the Alteryx Authentication Service.
Enable Request Signing: For IDPs that require request signing, you can enable the Enable Request Signing setting. This setting requires a valid signed certificate with an associated RSA private key to be installed in the Windows Certificate Store.
SSL/TLS Certificate Hash: Once you have your certificate and private key installed, provide the unique hash for the SSL/TLS certificate.
Verify IDP: Select to open a browser window, log in, test the IDP configuration, and set the default Server administrator.
Set a Default Gallery Administrator for SAML
A Gallery (Server) administrator account has to be created to administer the site (manage users, workflows, and more). For SAML authentication, select Verify IDP to test the IDP configuration and populate the field with IDP credentials.
You are now logged in as the Server administrator. You are now ready to add Server users. Go to Add Server Users.